SecureDNS and Log4j vulnerability
In recent days, security news has been dominated by a major new leak that could allow hackers to access the servers of companies. It concerns a vulnerability in Log4j: logbook software used by Apache web servers to keep track of things like changes and error messages. This vulnerability enables hackers to break into the servers of companies. The most common domains or IP addresses used as part of the scanning or reading of data are known malicious domains.
When the Log4j application parses these logs and encounters the string, the bug will force the server to make a callback, or request, to the URL listed in the JNDI string. Threat actors can then use that URL to pass Base64-encoded commands or Java classes to execute on the vulnerable device.
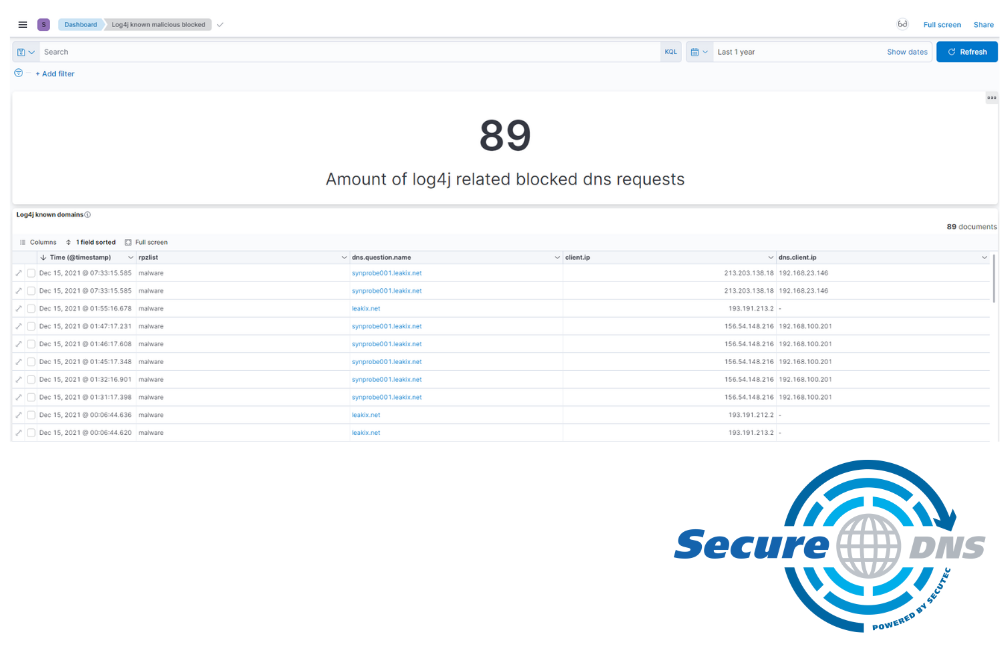
BUT all these domains were already known as malicious domains by Secutec SecureDNS and therefore blacklisted. Our Secutec SecureDNS customers are protected against the vast majority of Log4shell vulnerability exploit attempts. Why? Because Secutec SecureDNS protects and blocks the outgoing traffic. You still need to install patches against this vulnerability, as soon as they become available, to permanently protect your environment.
Want to know more about SecureDNS? https://www.secure-dns.eu/